A Beginner’s Guide to Setting Up a DIY Proxy Server on a Raspberry Pi
Dive into the world of do-it-yourself proxy servers, a powerful tool that can enhance online privacy security and even unlock content restrictions! I’ll walk you through the intricacies of servers, unraveling the tech jargon to make it accessible for everyone, from seasoned developers to curious beginners. Let’s start right now!
What is the Raspberry Pi?
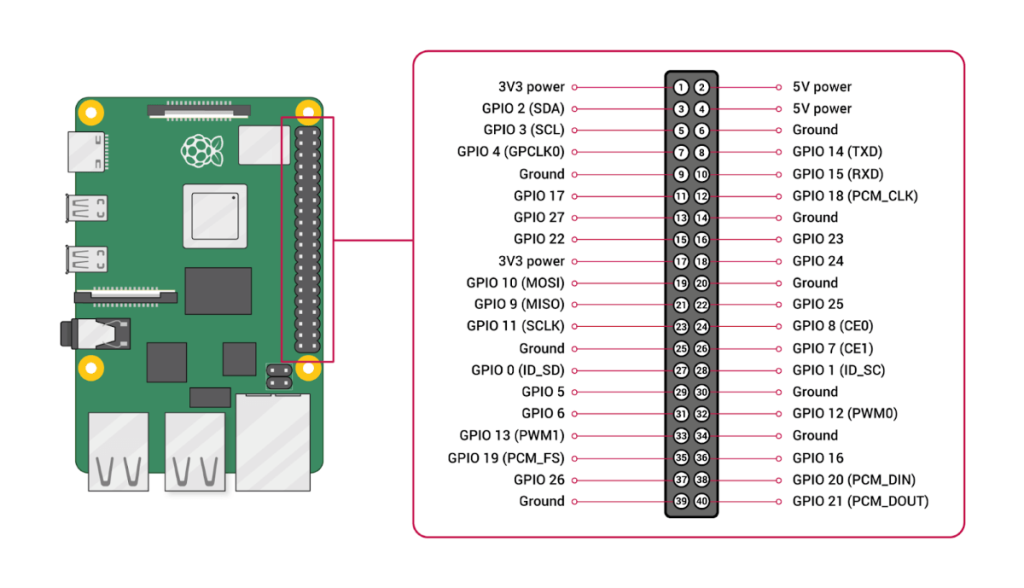
The Raspberry Pi, a versatile single-board computer, has become a cornerstone of do-it-yourself computing. Designed with affordability and accessibility, this credit-card-sized marvel boasts robust features, including USB ports, HDMI output, GPIO pins for hardware interfacing, and various models catering to different performance needs.
Its affordability, extensive community, and open-source ethos make it an attractive choice for tech enthusiasts, developers, and hobbyists. From developing custom solutions to embarking on creative projects, the Raspberry Pi provides a flexible foundation for various applications, setting the stage for our exploration into constructing a DIY proxy solution.
Understanding Proxy Servers
These are intermediaries between your device and the internet, enhancing online security, privacy, and performance. Connecting through a proxy reroutes your requests, masking your IP address for increased anonymity.
Beyond privacy, proxies offer content filtering to control website access and enable organizations to manage internet usage effectively. Caching mechanisms in such servers also contribute to bandwidth savings by storing frequently accessed content locally, leading to faster load times.
To use a proxy, configure your device to connect through it by specifying the proxy’s IP address and port. DIY proxy servers allow personalized control, offering a customizable solution for your online needs.
Learn more!
Prerequisites
Before setting up your DIY proxy solution on a RaspberryPi, ensuring you have the necessary prerequisites is crucial.
Firstly, a basic understanding of Linux commands will be beneficial, as the Raspberry Pi typically runs on Linux-based operating systems.
Additionally, having a microSD card with sufficient storage capacity (at least 16GB recommended) is essential for installing the operating system and other software. Addressing these prerequisites lays a solid foundation for a smooth and successful DIY proxy solution setup experience.
1. Choosing the Right Model
The Raspberry Pi lineup includes various models with unique features. The Raspberry Pi 4, equipped with more powerful hardware, including multiple USB ports and higher RAM capacity, is ideal for resource-intensive tasks. For users seeking a balance between cost and performance, the Raspberry Pi 3 remains a solid choice, offering dependable processing power at an affordable price point.
The Raspberry Pi Zero W is a consolidated option for more budget-conscious projects, sacrificing some processing capabilities for its smaller form factor and lower cost. Ultimately, the choice depends on the demands of your proxy solution usage, with the RaspberryPi 4 recommended for users requiring higher performance, the RaspberryPi 3 for a balanced approach, and the RaspberryPi Zero W for lightweight applications.
2. Installing Raspbian
Installing it, formerly known as Raspbian, is the crucial step in preparing your Raspberry Pi for the setup. Here’s what you need to do:
- Download the latest OS image from the official website for installation.
- Utilize a tool like Etcher to flash this image onto a microSD card, serving as Pi’s primary storage.
- Insert the prepared microSD card into the computer, power it up, and follow the user-friendly installation wizard.
This wizard lets you personalize language, keyboard layout, and password settings. Once completed, you’ll have a stable operating system to build your DIY proxy solution.
3. Installing and Updating Software
With the Raspberry Pi OS up and running, the next crucial step is installing and updating the necessary software components. Begin by opening a terminal and running a system update to ensure you have the latest packages. This command will help: sudo apt update && sudo apt upgrade -y.
That ensures your Raspberry Pi OS has the latest security patches and enhancements. Following the update, install the required software packages for your setup. For instance, if you’re using Squid, install it with sudo apt install squid.
Adjust configurations in the respective configuration files, typically in the /etc/ directory, to tailor the software to your needs. Regularly update your installed software with the latest features and security fixes. Maintaining up-to-date software on your computer ensures a secure and optimized environment.
4. Installing and Configuring
Now that your computer is armed with the required software, it’s time to install and configure the server, a critical component of your DIY setup. If you’ve opted for Squid as your proxy solution, modify its configuration file located at /etc/squid/squid.conf to align with your preferences. Configure settings such as allowed IP addresses, ports, and access controls to tailor the proxy server to your specific needs. Remember to restart the Squid service after making changes: sudo service squid restart.
For additional security, consider implementing authentication mechanisms to control access. That ensures that only authorized users can utilize your proxy server. Once configured, your computer transforms into a personalized proxy server, ready to enhance your online privacy, security, and content accessibility.
5. Testing
With your DIY proxy solution configured, thorough testing ensures it functions seamlessly before active use. Adjust your device’s network settings to point to the Raspberry Pi’s IP address and designated port as the proxy solution. That can be done in your device’s network settings or browser preferences. Next, navigate to a website and confirm it loads correctly, indicating successful proxy server integration. Pay attention to errors, unexpected behavior, or sluggishness that may indicate configuration issues.
To further validate functionality, check the Squid logs for real-time insights: sudo tail -f /var/log/squid/access.log. This command allows you to monitor incoming requests and responses. Ensure the logs reflect the expected activity corresponding to your testing.
For a comprehensive evaluation, try accessing websites from different devices and networks, confirming consistent performance. By meticulous testing, you guarantee a reliable and effective DIY server, enhancing your online experience with heightened privacy and security.
6. Configuring Client Devices
You can start setting up client devices to connect through a server by accessing your device’s network settings or browser settings. There, you will find the option to configure a server. You need to enter the IP address of your RaspberryPi and the designated port you configured during the proxy server setup.
Ensure attention to the following key aspects…
- Proxy Type: Choose the appropriate type, often HTTP or HTTPS, based on your configuration. That ensures proper communication between your device and the proxy solution.
- Port Configuration: Double-check that the port specified in your client device matches the one you configured on your RaspberryPi. Consistent port settings are essential for a seamless connection.
- Authentication Settings: If you’ve implemented authentication on your server, enter the correct username and password in your client device settings. This step is crucial for authorized access.
Additionally, consider configuring specific applications to use the proxy server if global device-wide settings are not preferable. This selective approach allows you to tailor the proxy usage to specific needs, optimizing performance and privacy for targeted activities. By configuring your client devices attentively and exploring application-specific settings, you establish a robust connection to your DIY proxy server, ensuring a personalized and secure online experience.
Troubleshooting Common Issues
The presence of common issues in your server may disrupt your online experience, leading to potential privacy and security concerns. I’ll guide you through troubleshooting these challenges, ensuring your server’s smooth and secure operation. Let’s delve into some common issues and their quick resolutions.
| Connection errors | Detection: Check for errors in the logs: sudo tail -f /var/log/squid/access.log.Resolution: Verify network configurations on both the RaspberryPi and connected devices. Ensure firewall settings permit traffic on the port. |
| Slow performance | Detection: Monitor Squid logs for delayed responses: sudo tail -f /var/log/squid/access.log.Resolution: Adjust Squid’s caching settings in /etc/squid/squid.conf to optimize performance. Also, ensure your RaspberryPi hardware meets the demands of proxy server usage. |
| Authentication issues | Detection: Look for authentication-related errors in the Squid logs.Resolution: Double-check username and password configurations in /etc/squid/squid.conf. Ensure proper authentication settings are applied. |
| Certificate errors | Detection: Browser warnings or errors during secure (HTTPS) connections.Resolution: Install and configure SSL certificates on your proxy server. Update the certificate paths in the Squid configuration file. |
| Server not responding | Detection: Unable to connect to the proxy server.Resolution: Restart the Squid service: sudo service squid restart. Check for any service-related errors in /var/log/squid/cache.log. |
Helpful Things to Remember
Here are some invaluable tips to streamline the process and optimize performance. These hints will guide you through a smoother configuration experience, from regular updates to prudent security measures.
- Regular Updates: Keep your RaspberryPi OS and proxy server software current. That ensures you benefit from the latest features, bug fixes, and security patches.
- Backup Configurations: Before making significant changes to your server settings, create backups of configuration files. This precautionary measure allows you to easily revert to a stable configuration if issues arise during experimentation.
- Monitoring Resources: Keep an eye on your RaspberryPi’s resource usage, especially if you opt for a model with limited computational power. Tools like Htop can provide real-time insights, helping you optimize performance.
- Security Measures: Enforce additional security measures, such as enabling firewalls and regularly reviewing access logs. That enhances the overall security of your proxy server setup.
- Documentation: Maintain thorough documentation of your setup, including configurations and any customizations made. This documentation proves invaluable for troubleshooting and replicating your setup in the future.
- Testing from Various Networks: Test your proxy server from different networks and devices to ensure compatibility and consistent performance across various scenarios.
- Consider SSL/TLS Encryption: If privacy is a top priority, consider configuring your proxy server to support SSL/TLS encryption. That will let you add an extra security layer to the data transmissions.
Conclusion
As you implement these configurations, remember the importance of staying updated, monitoring your setup, and fostering community engagement. Your RaspberryPi is a versatile platform, merging accessibility with customization.
Whether you’re a seasoned developer or an eager enthusiast, may your digital ventures be fortified by the security and personalization afforded by your RaspberryPi-powered proxy server. I wish you good luck, and I am sure you will succeed.
